Month: April 2024

How Bare Metal Servers Can Contribute to a Sustainable IT Strategy
In today’s environmentally conscious world, businesses are striving to minimize their carbon footprint. Surprisingly, IT infrastructure plays a significant role in overall energy consumption. While offering flexibility, traditional virtualized environments can lead to resource waste and higher energy demands.
At HorizonIQ, we’re committed to empowering businesses with sustainable IT solutions. Bare metal servers offer a compelling alternative that can significantly contribute to a more eco-friendly IT strategy.

Unlocking Efficiency: Bare Metal’s Green Potential
Bare metal servers are dedicated physical servers assigned to specific tasks or applications. This approach offers several key advantages over virtualized environments:
- Reduced Energy Consumption: Unlike virtualized environments with a hypervisor layer and multiple virtual machines sharing resources, bare metal servers eliminate unnecessary overhead. This streamlined approach translates to lower overall energy consumption for the same workload.
- Resource Optimization: Bare metal servers dedicate resources to specific tasks, eliminating the “resource contention” that can occur in virtualized environments. This optimized utilization reduces the need for additional servers and their associated energy demands.
- Minimized Cooling Needs: Efficient hardware utilization in bare metal servers translates to lower heat generation. This can significantly reduce the need for extensive cooling infrastructure, leading to potential energy savings and a smaller environmental footprint.
Embrace a Sustainable IT Future with HorizonIQ
We understand the importance of responsible IT practices. Our bare metal solutions are customizable to your needs, delivering peak performance while also prioritizing sustainability. By optimizing energy efficiency, resource allocation, and cooling requirements, bare metal servers can significantly contribute to a more sustainable IT strategy.
Ready to power up your sustainability efforts? Explore how our bare metal servers can help achieve your IT goals. Together, we can build a greener future for all.
Explore HorizonIQ
Bare Metal
LEARN MORE
Stay Connected

Firewalls 103: Unlocking Advanced Security with Application Layer Inspection
Continuing our firewall series, we explore Application Layer Inspection (ALI), a powerful security feature often missing from basic firewalls. Be sure to check out our articles about Network Address Translation (NAT) and ACL Rules to learn about their roles in network security.
In the world of cybersecurity, many out-of-the-box firewalls lack the advanced feature of application layer inspection (ALI). This critical capability is often an additional licensed offering, adding an extra layer of defense against sophisticated threats.
ALI: Going Deeper Than Packet Headers
Advanced firewalls, such as those used by HorizonIQ, take security to the next level by enabling application layer inspection. While traditional firewalls inspect packet headers for source and destination information, ALI dives deeper. It analyzes the actual contents of data packets, identifying specific applications, protocols, and even malware signatures. This granular control allows for highly effective threat detection and prevention.
HorizonIQ & Palo Alto Firewalls: A Powerful Security Combination
Palo Alto firewalls, a cornerstone of HorizonIQ’s security infrastructure, offer application layer inspection through the “Threat Prevention” add-on. This feature actively seeks known signatures of hacking and malware, fortifying your defense mechanisms.
But Palo Alto’s security doesn’t stop there. “WildFire” unlocks a comprehensive suite of advanced threat protection capabilities:
- Dynamic Analysis: Execute suspicious files in a secure sandbox to observe behavior and identify malicious activity.
- Malware Detection: By analyzing file behavior and characteristics, WildFire identifies known and unknown malware variants, including polymorphic and metamorphic strains, using signature-based detection and machine learning algorithms.
- Zero-Day Protection: Effectively combat zero-day exploits, vulnerabilities unknown to vendors or lacking available patches, through dynamic analysis, preventing harm before it occurs.
- Threat Intelligence: WildFire continuously updates its threat intelligence database, leveraging a global network of sensors to proactively protect against emerging threats.
- Automatic Remediation: Swiftly respond to detected malicious files. WildFire automatically generates signatures and updates to Palo Alto Networks’ security devices, containing and mitigating cyber attacks in real-time.
- Integration with Security Ecosystem: WildFire seamlessly integrates with various security technologies and platforms, sharing threat intelligence to strengthen the overall security posture. It collaborates with SIEM systems, threat intelligence platforms, and endpoint protection solutions.
- Advanced Reporting and Analysis: WildFire provides comprehensive reports and analysis dashboards, offering insights into detected threats, affected systems, and the overall security posture of the organization. This enables informed decision-making and proactive security measures.
HorizonIQ: Your Guide to Enhanced Network Security
If your security needs surpass simple ACL rules, HorizonIQ’s expert staff can help you harness the power of Application Layer Inspection for unparalleled network defense. Discover a new level of security and keep your organization safe from evolving threats.
Explore HorizonIQ
Bare Metal
LEARN MORE
Stay Connected
Infrastructure in a Box: Your One-Stop Shop for Streamlined IT Infrastructure
Gone are the days of piecing together IT infrastructure component by component. HorizonIQ’s Infrastructure in a Box streamlines the process, delivering a pre-configured solution that caters to your specific business needs.
What is Infrastructure in a Box?
Infrastructure in a Box is our comprehensive IT infrastructure package that bundles essential components like compute, network, storage, and security resources. HorizonIQ’s expert technicians meticulously configure these elements to seamlessly integrate and function as a cohesive unit.
Benefits of Infrastructure in a Box:
Faster Deployment: Infrastructure in a Box eliminates the need for lengthy procurement and configuration processes. Pre-configured solutions allow for rapid deployment, minimizing downtime and getting your business up and running quicker.
Reduced Complexity: Managing a complex IT infrastructure can be overwhelming. Infrastructure in a Box simplifies management by providing a unified solution, reducing the burden on your IT staff and allowing them to focus on core business objectives.
Enhanced Scalability: Infrastructure in a Box solutions are designed to scale alongside your business needs. Whether you require additional processing power, storage capacity, or network bandwidth, Infrastructure in a Box can be easily adapted to accommodate growth.
Cost-Effectiveness: Infrastructure in a Box offers a cost-efficient approach to IT infrastructure. Predictable pricing and bundled solutions eliminate the risk of overspending on unnecessary hardware or software licenses.
Why Choose HorizonIQ’s Infrastructure in a Box?
At HorizonIQ, we understand that every business has unique IT requirements. We take the time to assess your specific needs and tailor an Infrastructure in a Box solution that aligns perfectly with your budget and operational goals.
Our Infrastructure in a Box offerings encompass a variety of industry-leading hardware and software components, ensuring optimal performance, reliability, and scalability. Additionally, HorizonIQ boasts a team of experienced technicians who will flawlessly configure and integrate your Infrastructure in a Box solution, ensuring a seamless transition and ongoing support.
Beyond the Box: Superior Support and Expertise
Our commitment extends beyond simply delivering a pre-configured solution. HorizonIQ provides ongoing support to ensure your Infrastructure in a Box continues to meet your evolving needs. Our team is readily available to address any technical issues, answer your questions, and provide expert guidance as your business grows.
If you don’t have the people or expertise to manage your infrastructure, you can rely on us to mange your Infrastructure in a Box solution for a flat monthly fee.
Unleash Your Potential with Infrastructure in a Box
Ready to streamline your IT infrastructure and empower your business for success? Learn more about our comprehensive Infrastructure in a Box solutions and discover how we can help you achieve your IT goals.
Explore HorizonIQ
Bare Metal
LEARN MORE
Stay Connected

Firewalls 102: Understanding Basic Filtering and ACL Rules
To continue our firewall series, we are delving into the fundamentals of basic filtering, a cornerstone of network security. Be sure to check out Part 1 for a deep dive into Network Address Translation (NAT).
Firewalls act as guardians, meticulously examining data packets traveling between your secure internal network and the wild world of the internet. Basic filtering allows authorized traffic to flow freely while blocking unwanted connections.
Demystifying Firewall Rules and ACLs
To control this traffic flow, firewalls leverage Access Control Lists (ACLs), essentially a set of rules dictating which traffic is allowed and which is denied. Each data packet carries information like source and destination IP addresses, along with the designated service (port) it uses. The firewall meticulously compares this information against each ACL rule, one by one. Here’s why the order of these rules is critical.
Breaking Down a Simplified ACL Rule:
- Source IP: Specifies the sender’s IP address (or a range of addresses).
- Destination IP: Specifies the recipient’s IP address (or a range of addresses).
- Service/Port: Defines the type of traffic (e.g., web browsing – port 80, secure browsing – port 443).
- ALLOW/DENY: Determines whether to permit or block the traffic.
- Comment: Provides a brief explanation for the rule’s purpose.
The below example shows a basic firewall rule set enabling a web server to communicate securely:
| Source IP | Destination IP | Service/Port | ALLOW/DENY | Comment |
| ANY | WebServer | Hypertext transfer protocol (http) / 80 | ALLOW | Allows anything to use unencrypted web protocol traffic to talk to the web server |
| ANY | WebServer | Hypertext transfer protocol secured (https) / 443 | ALLOW | Allows anything to use encrypted web protocol traffic to talk to the web server |
| ANY | ANY | ANY | DENY | Denies any traffic that isn’t defined above. AKA “implicit deny” |
A misplaced rule can have unintended consequences, highlighting the importance of order. Additionally, the final “deny” rule acts as a safety net, blocking any unrecognized traffic.
Stateful Inspection: A Powerful Tool with Nuances
Beyond ACLs, firewalls utilize stateful inspection to track connection information, ensuring data flows consistently in and out of the same interface. This feature, while powerful, demands careful configuration. We share a real-world scenario highlighting the significance of order in rule application.
Stateful inspection, despite occasional challenges, is a crucial tool to thwart hacking attempts. Our experienced technical staff at HorizonIQ specializes in optimizing rules and order, ensuring your managed firewall operates securely and efficiently.
Empower Your Network Security with HorizonIQ
Partner with HorizonIQ to leverage our managed firewall services and benefit from our dedicated technical support team. Learn best practices and implement a robust security posture for your organization.
Stay tuned for future articles in this series where we explore firewalls and their functions, helping you make informed network security decisions.
Looking for more IT solutions? Explore our comprehensive suite of services.
Explore HorizonIQ
Bare Metal
LEARN MORE
Stay Connected
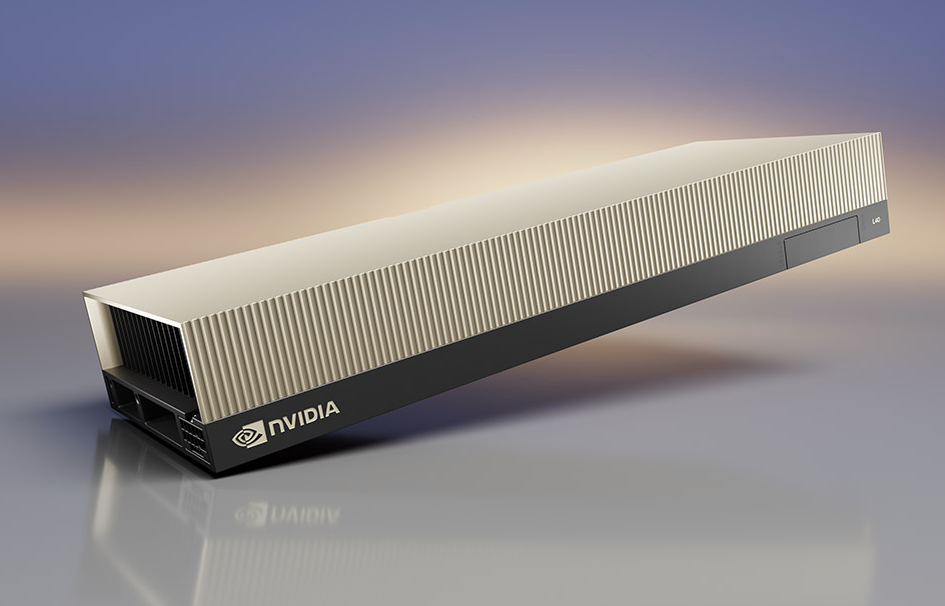
Bare Metal vs. Public Cloud: Peak Performance for AI Applications
The ever-evolving landscape of Artificial Intelligence (AI) demands a robust hosting infrastructure to guarantee peak performance, scalability, and cost-effectiveness. While the public cloud offers undeniable flexibility, bare metal hosting from providers like HorizonIQ provides distinct advantages tailored specifically for the demanding nature of AI applications.
Let’s delve into the key benefits of hosting AI workloads on bare metal compared to the public cloud.
Unparalleled Performance and Low Latency
AI applications, especially those involving deep learning and high-throughput computing, require exceptional responsiveness and minimal delays. Bare metal hosting offers dedicated hardware resources, bypassing the virtualization layer that can introduce overhead. This translates to:
Superior computational power: Dedicated resources ensure faster processing and reduced inference times.
Enhanced model training efficiency: Eliminate bottlenecks for faster model development and training cycles.
Improved overall application performance: Critical for real-time AI applications like autonomous vehicles, financial trading algorithms, large language models (LLMs), and healthcare diagnostics.
Tailored Infrastructure for Demanding Workloads
Bare metal hosting offers unparalleled control and customization over the hardware and software stack. AI developers can fine-tune the infrastructure to their specific models’ needs, optimizing resource utilization for accelerated compute tasks. This level of control is particularly beneficial for:
Complex AI workloads: Fine-tune hardware configurations for specialized needs.
Low-level optimizations: Unrestricted access empowers researchers and data scientists to push the boundaries of innovation.
Prioritizing Data Privacy and Security
Data privacy and security are paramount for AI applications handling sensitive information. Bare metal hosting allows organizations to:
Maintain complete control over data: Minimize the risk of exposure or unauthorized access inherent in multi-tenant public cloud environments.
Ensure regulatory compliance: Meet industry standards and instill confidence regarding data integrity and confidentiality.
Cost-Efficiency for Predictable Workloads
While the public cloud offers scalability and pay-as-you-go models, bare metal hosting can be more cost-effective in specific scenarios. Here’s why:
Eliminate virtualization overhead: Reduce costs associated with hypervisor licensing, instance sizing, and resource contention.
Predictable pricing: Flat, predictable pricing from HorizonIQ avoids variable costs associated with public cloud usage.
Optimized cost-performance ratio: Organizations with consistent or high-performance workloads benefit from long-term cost savings.
Navigating Compliance and Regulatory Requirements
Certain industries face stringent data privacy, sovereignty, access, and auditing regulations. Bare metal hosting offers greater flexibility in adhering to these mandates, making it an attractive option for AI applications in highly regulated sectors like finance, healthcare, and government.
Choosing the Right Infrastructure for AI Success
While the public cloud offers convenience, bare metal provides distinct advantages for performance-critical AI workloads. By carefully evaluating factors like data privacy, regulatory compliance, and workload demands, organizations can make informed decisions about the hosting solution that aligns best with their AI objectives, leading to success in the era of AI-powered innovation.
Uncover the unmatched performance of AI on Bare Metal. Learn more about our solutions.